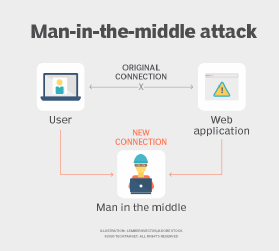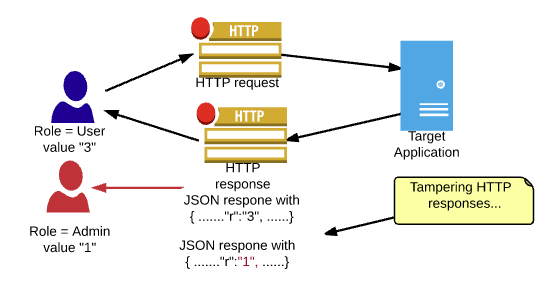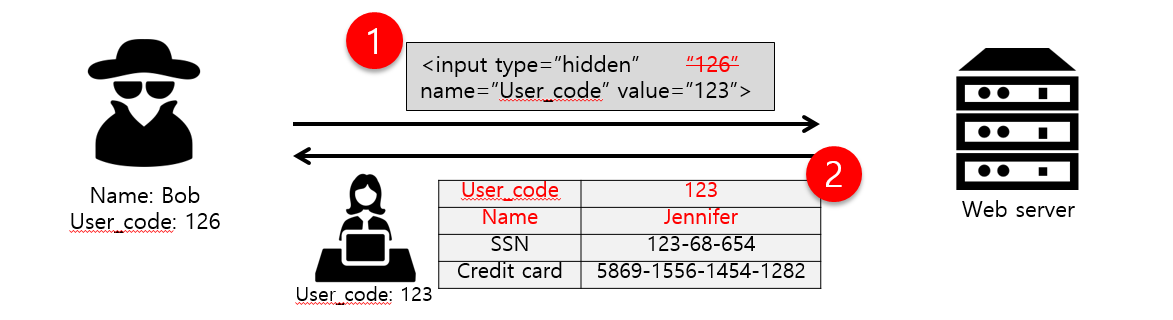
What is Parameter Tampering. Parameter Tampering: Special Characters | by MRunal | InfoSec Write-ups

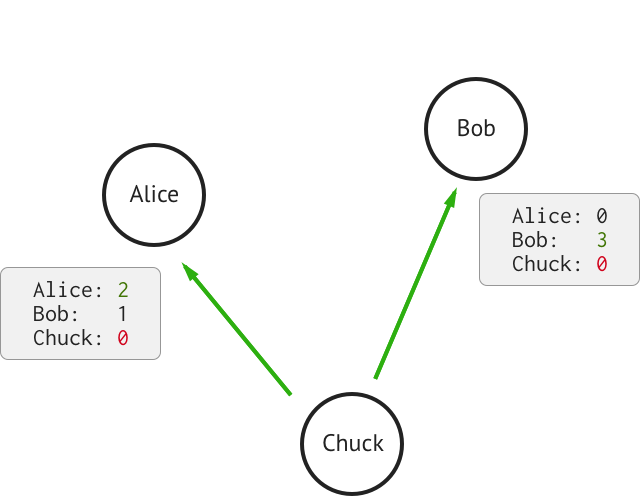
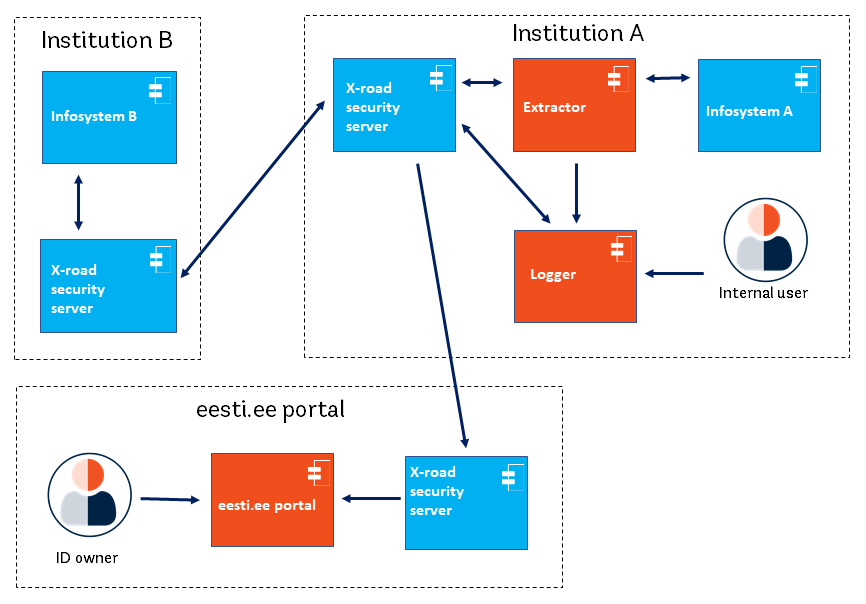
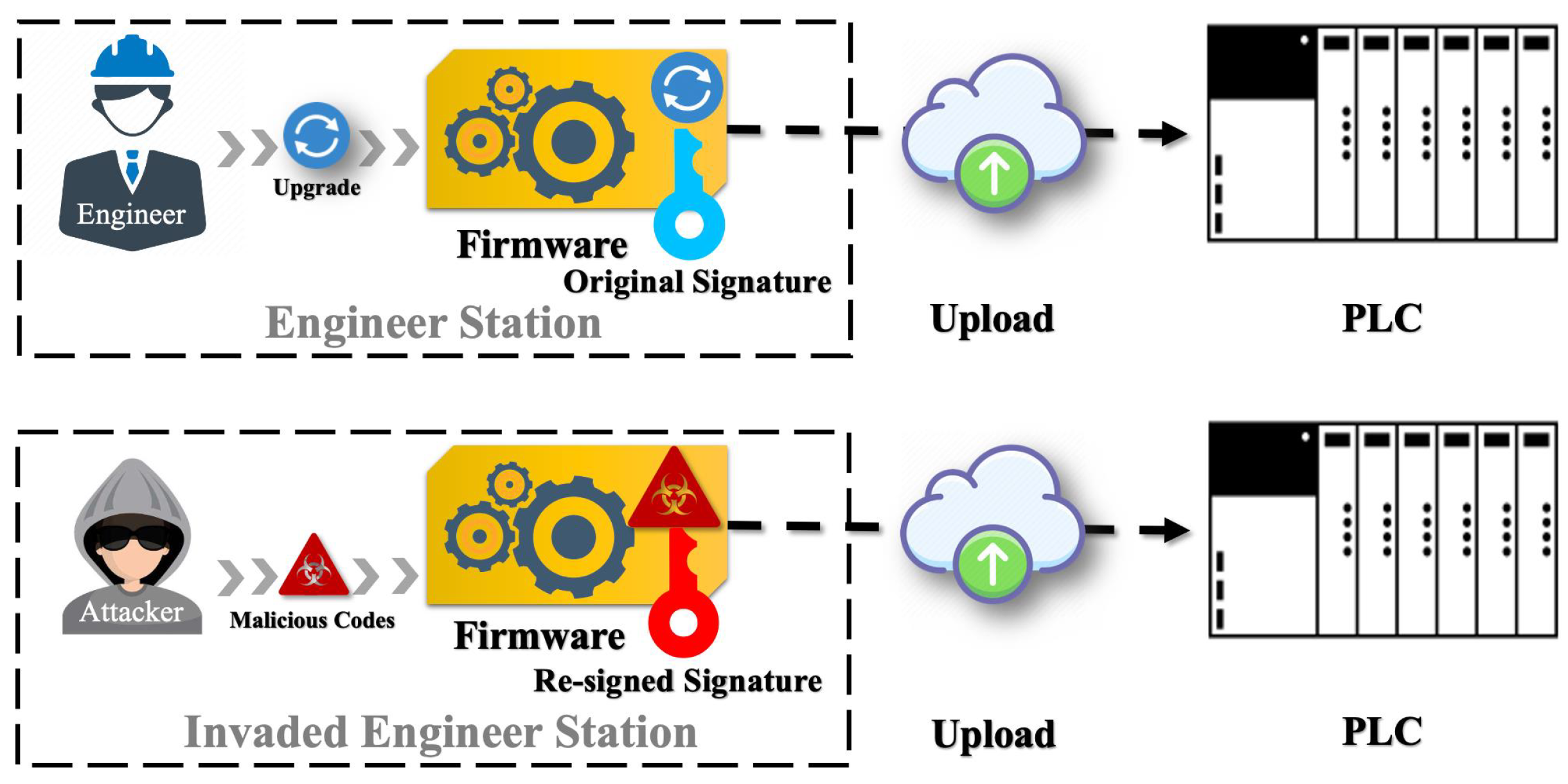
An example of a configuration data tampering attack 3.3. Variable data... | Download Scientific Diagram

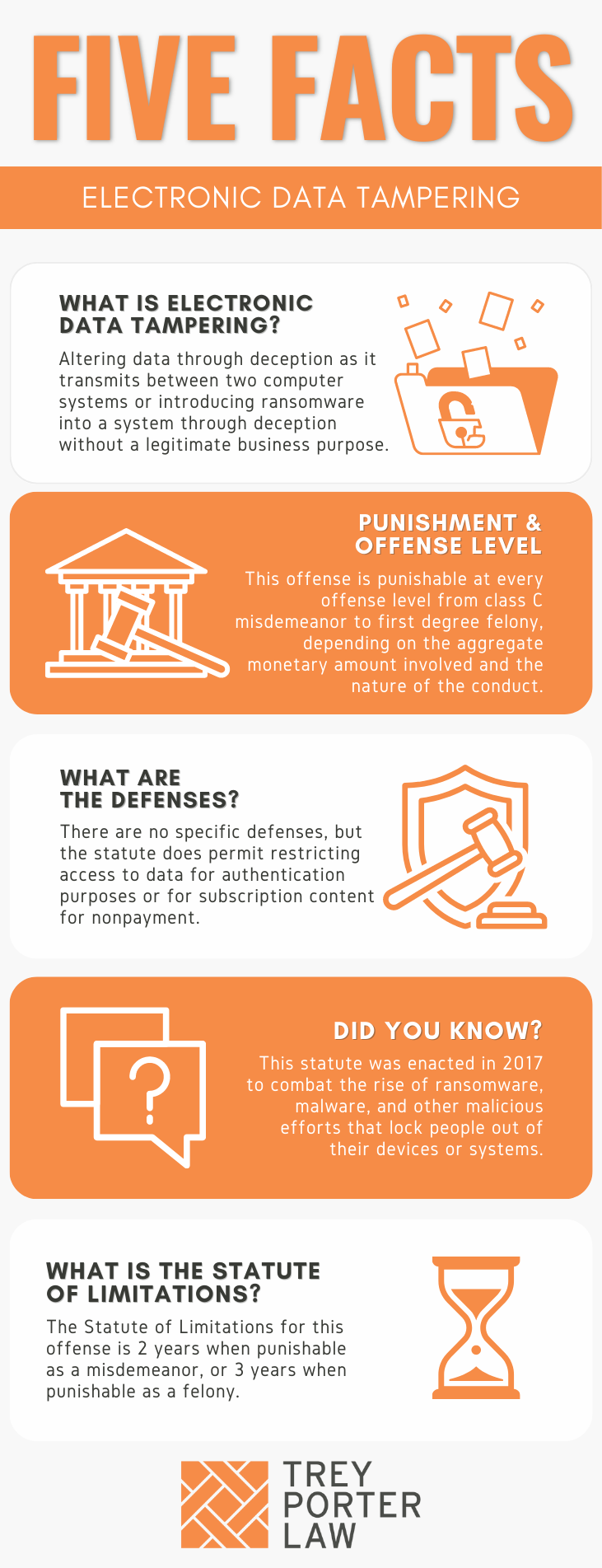
Database Tampering and Detection of Data Fraud by Using the Forensic Scrutiny Technique | Semantic Scholar